Government and military forces around the globe that make use of ubiquitous civil GSM networks are being jeopardized when sailing from port to port — fraudulent cell towers are able to intercept and spoof messages and calls, resulting in personnel privacy and mission operations being compromised.

These kind of events typically occur in frontiers between countries or strategic areas where hacking activities are intense over one of the most accessible devices, a soldier’s cellphone/smartphone.
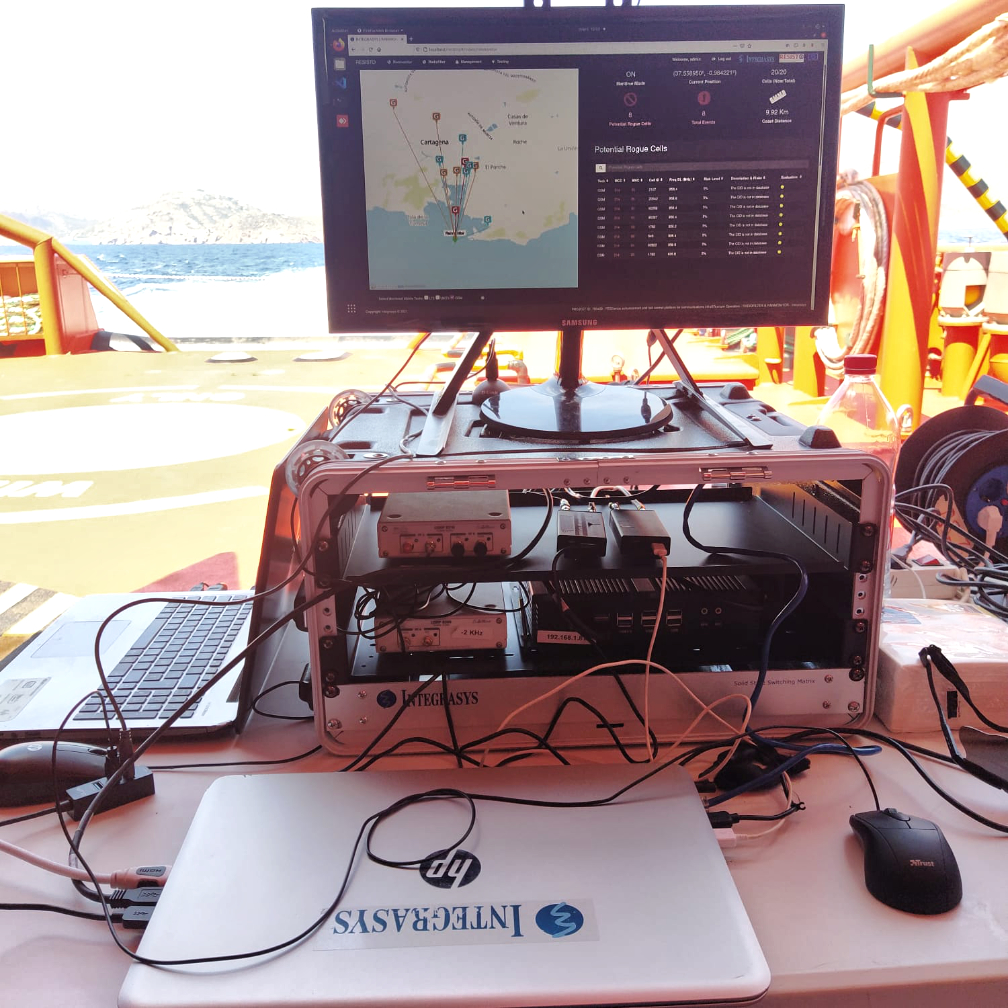
In the RESISTO (RESIlience enhancement and risk control platform for communication infraSTructure Operators) project funded by the European Commission, Integrasys has developed RANMONITOR for fraudulent cell towers detection that has been recently tested satisfactorily during the Spanish Navy MARSEC21 exercise.
A fraudulent cell installed aboard the OPV Infanta Cristina was successfully detected by RANMONITOR, identifying the threat and properly differentiating it from the rest of the legitimate cell stations deployed on the close coast. With such a capability, it is possible to make certain that one’s own forces´ mobile phones do not connect to the pirate station and that minimizes attack possibilities.

If any cellular phone connects to such an illegitimate station, Integrasys tools can record all of the signaling, calls and messages exchanged for further analysis. One of the most interesting key factors of this exercise was to match end-user needs with software tools providers to understand better government needs firsthand and to customize such a solution to each end-user processes and operations.
Work on RESISTO project has resulted in a tool that makes government networks more secure and resilient, with an easy-to-use interfaces for forces operating in the field. The RANMONITOR product is designed to protect 2G as well as 3G/4G and, in the future, future 5G, in both fixed and mobility scenarios, as demonstrated in MARSEC. These solutions will help governments around the globe be far less compromised and more secure in mitigating hacking on a soldier’s smartphone.